326 - 14 March 2024 - Utilizing Rapidly Alternating Coulomb Force Line Generation in Support of Transient Liquefaction of Solid Material for Purposes of Deep Earth Exploration, Mining without Drilling and Deep Munition Penetration
Physical Science Abstracts Mysteriously Not Allowed by Vixra et. al.
Page 7 - For the science geek in everyone, Live Science breaks down the stories behind the most interesting news and photos on the Internet.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
327 - 15 March 2024 - The Use of Energetic Means to Provoke Undesired Detonation of Explosive Torpedo Warheads Within Targeted Ships Using Teams of Miniature Stealthy Drone Submarines Equipped with Soliton Emitters
Attachments
SAM.gov
Looks like they're utilizing 12 September 2023 except they use traunches of misleading language in this, as per usual.
They keep referring to it as a "filter" but it is nothing quite so simple. AESA, which is a 20+ year old technology, has been improved over the years and works by emitting RADAR signals on a rotating modulations and listening only on certain frequencies at certain times and ignoring all other signals. The ability to jam such a system is predicated upon creating high amplitude signals which are rotated at a rate that is substantially greater than the AESA rotational rate. If signals are transmitted on all possible frequencies, rotation is not necessary to support jamming.
I've come up with a few different possible solutions to this problem of the jamming, one of which is to use layered metamaterials to act as a physical gating mechanism (although I feel as though filtering according to angular momentum is a cleaner approach and I have explained exactly how we can do this.) As for the metamaterial gating approach, the concept is actually to both block and permit EM through shielded and unshielded areas of a receiver, respectively.
It is much easier to suss out the content of an authentic signal in a high-noise environment when one knows in advance exactly when a signal will be received. If a receiver is programmed in advance to expect signals on a certain schedule (and they are transmitted on a schedule) an adversary would eventually adapt and focus their jamming during those windows (millisecond or less) during when signals are sent e.g. telling a drone to make a turn or fire a missile.
The use of tailored metamaterial layers of up to dozens or perhaps hundreds of layers of thickness in which each layer has unique properties enables only specific, complex signal patterns to make it through the shielded portions of a receiver. Only when a signal authenticity "tag" is sent will actual data be sent to a drone or other platform. False "tag" codes would be sent continually except when actual data is to be sent. When an authentic tag code is sent, authentic data is transmitted to the platform in the RF-denied environment. The noise-mitigation software onboard the platform (entirely automated) would use this information concerning the expected timing of the authentic signal in order to "focus in" on that window of time. Repeated signals would be sent (also tagged) and after a series of re-transmissions in which the platform can know, beyond a doubt, that a valid instruction is being sent during those timeframes, the ability to analyze repeated "noisy" versions of authentic signals greatly enhances the ability of automated software-based noise reduction to be effective.
Is it a filter? No. It is a kind of a cue or prompt that enables the software-based noise reduction software to work more effectively. It is also being used without my consent as I have never sent this information to them, sold it, or any other such thing.
It is remarkable the number of specific concepts which have been flat-out stolen in recent months. What do the Ph.D.s who work for them do all day? Do they have no ideas of their own?
328 - 17 March 2024 - Utilization of Precision Optical Measurement of Individual Photons Subject to Known Influences to Evaluate Any Segment of Pi Number Without Need to Calculate Previous Numbers
Attachments
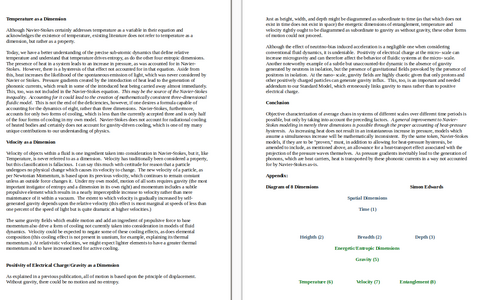
329 - 19 March 2024 - Reconciling Navier-Stokes Inequality: Delay Between Introduction of Heat and Pressure Response - Four Spatial and Four Energetic Dimensions in Which Gravity is Prerequisite for All Other Entropic Effects
Attachments
It's good to get some positive feedback. Where are you from, if you don't mind my asking? I shared this thread with some folks in Sweden and it seems to be gaining momentum, although I'm not sure which path it took to gain that momentum.Thank you for being so generous with your knowledge. It's truly appreciated.
331 - 23 March 2024 - Evolutionary Function of Enhanced Probability of Embryo Sex Being Set as Male in Humans and Hypothesis Concerning Mechanism Through Which This Bias in Probability Is Introduced
Attachments
332 - 25 March 2024 - Augmenting Space-Based-Soliton (SBS) Submarine Detection Systems with Improved Covert Mobile Sonobuoy Systems for High-Precision Fix on Quiet Adversary Submarines
Attachments
335 - 28 March 2024 - Method for 7.3 μm Water-Vapor Imaging of Granular Ground-Level Vapor Anomalies Which Mitigates Interference from Above Layers to Enable New Intelligence Insights Dependent Upon High-Contrast Imaging of Human-Introduced Moisture
Attachments
336 - 29 March 2024 - Mechanism Provoking Behavioral Changes in Patients with Chronic Toxoplasmosis Infections of the Brain May Be Related to Toxo Depletion of Esterases
Attachments
337 - 31 March 2024 - Linkages Between Matter in the Present with Old Gravity Remaining in Temporal Past May Resolve the Grandfather Paradox with Concept of Self-Consistent Ordered Matter Reconfiguration
Attachments
339 - 5 April 2024 - Collimated Phononic Lines for Non-Thermal (Acoustic) Chemical Catalysis
Attachments

‘Critical tool’: New whale detection technology being used in B.C. waters | Globalnews.ca
Ocean Wise has announced new underwater microphones will be used to detect whales in B.C. waters that will work to mitigate ship-whale collisions.
Up in SOSUSland they are now "listening for whale-like noises" and triangulating the source of these noises as a matter of course.
(see 25 March 2024)
Interesting, isn't it?
340 - 11 April 2024 - Combining Spinless Photon Magnetometers with Magnetic Footprint Amplification of Received Light for Revolutionary Divergent Moment Photonic Sensors (DMPS)
Attachments
345 - 19 April 2024 - Anti-Personnel Anti-Electronic X-Ray Pulse Mechanism Driven by Explosive Blast Wave Energy Actuated Versus High-Thickness Casing Undergoing Rapid Cycling of Coulomb-Driven Liquefaction-Resolidification
Attachments
Similar threads
- Replies
- 2
- Views
- 579
- Replies
- 4
- Views
- 1K
- Replies
- 3
- Views
- 6K
TRENDING THREADS
-
What is a living individual and is it naturally universally mobile?
- Started by tonylang
- Replies: 138
-
-
Important Astronomy - No elliptic orbit and relativity break through
- Started by TheBox
- Replies: 63

Live Science is part of Future plc, an international media group and leading digital publisher. Visit our corporate site.
© Future Publishing Limited Quay House, The Ambury, Bath BA1 1UA. All rights reserved. England and Wales company registration number 2008885.